Securing IoT Devices Risks and Best Practices for Businesses Circuit Diagram
BlogSecuring IoT Devices Risks and Best Practices for Businesses Circuit Diagram Educate users about the importance of IoT security and best practices for safeguarding devices. Training should include recognizing phishing attempts, securing home networks, and reporting suspicious activity. 7. Develop a Comprehensive Security Policy. Create a security policy that outlines the procedures and protocols for securing IoT devices.
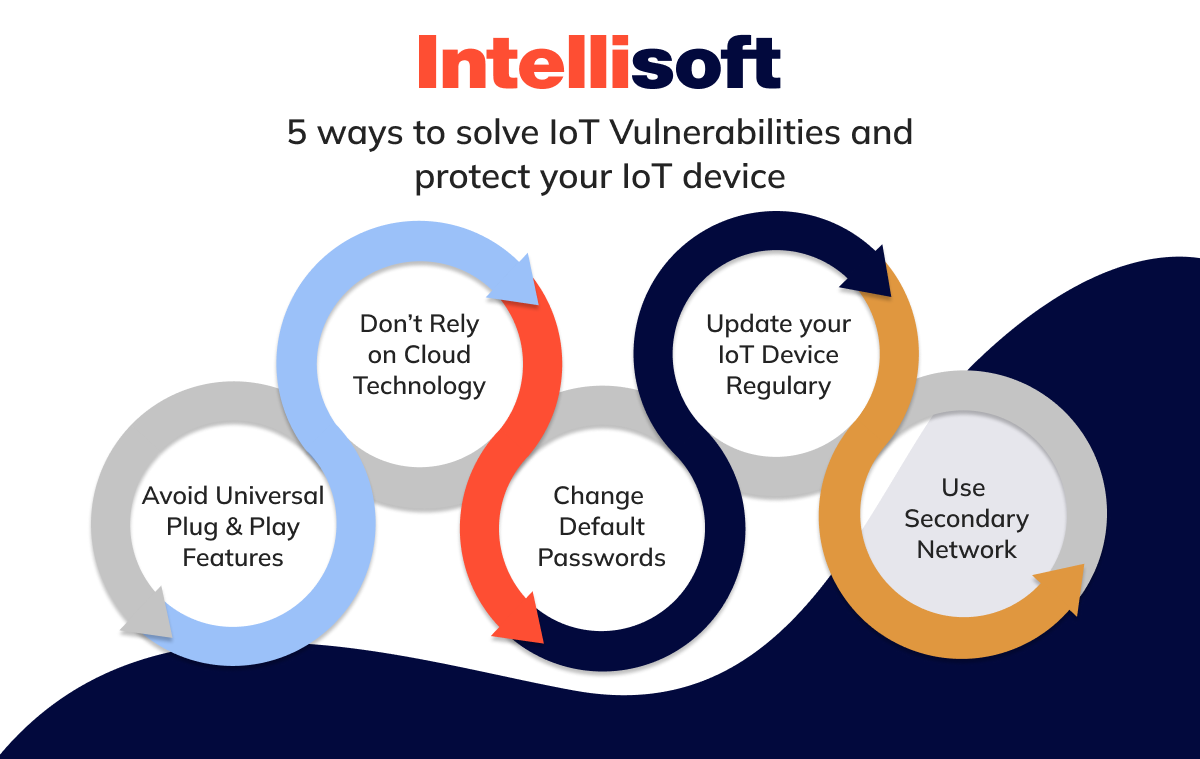
For a deeper dive into security practices, check out our Guide to Data Encryption and Securing Digital Devices: Best Practices. Implementing a Comprehensive IoT Security Plan. Holistic Approach to IoT Security. Securing IoT devices, whether at home or for your business, starts with one crucial step: removing weak default passwords. The IoTSF Best Practice Guidelines cover various aspects of IoT security, including secure development, secure deployment, data privacy, and the management of security incidents. Each section provides clear and concise recommendations, which can be easily followed by IoT professionals and organizations.

8 Best Practices for Securing the Internet of Things (IoT) Circuit Diagram
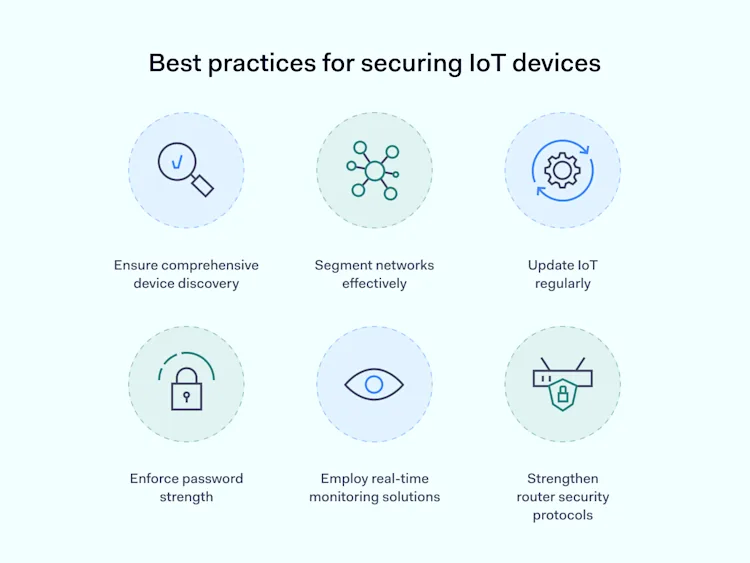
This includes providing secure connectivity between devices, data storage, and IT environments, whether on premises or in the cloud. Then, IoT security becomes a matter of policy enforcement. The following section provides specific recommendations for IoT security best practices starting with how to develop an effective IoT security strategy.

Therefore, there are multiple security practices that are used by individuals to maintain the safety and security of their devices. Name the best IoT security practices. Some of the best Internet of Things security practices are: regularly patch and update the IoT devices; carefully manage the device inventory; isolate the IoT devices; monitor
Security best practices - Azure IoT Circuit Diagram
To help prioritize IoT Zero Trust investments, you can use the Industry IoT Consortium's (IIC) IoT Security Maturity Model to help assess the security risks for your business. Zero Trust principles and best practices for end-to-end security. When designing an IoT solution, it is extremely important to identify and understand potential threats 8 Best practices to improve your IoT security . Securing the IoT infrastructure is critical, but it requires a robust strategy to effectively secure data in the cloud and protect data integrity in transit. Here are some of the best practices to improve IoT security for your organization. 1. Track and manage your devices
The following diagram shows a high-level view of the components in a typical cloud-based IoT solution. This article focuses on the security of a cloud-based IoT solution: You can divide security in a cloud-based IoT solution into the following three areas: Device security: Secure the IoT device while it's deployed in the wild.